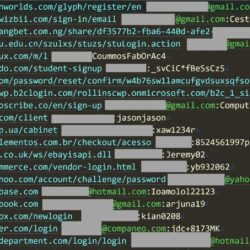
Breaking out of kiosk environments using keyboard media buttons via a BadUSB type attack
In early 2023 an awesome colleague (Andreas) spoke about an incident response case featuring thugs plugging a media keyboard into an ATM, and breaking out of its ATM kiosk software to install malware causing it to dispense $$$. This prompted me to spend some time during spring and summer of 2023 looking into Consumer Control, Read more about Breaking out of kiosk environments using keyboard media buttons via a BadUSB type attack[…]